Blog
Where Do Deleted Files Go?
It may seem like the file is gone for good when you delete it from your computer. However, the truth is more complicated than that. A deleted file doesn’t really disappear from your hard drive; it stays there until new data fills up the space it occupied. This process might be hard to understand for…
Read More6 Reasons Why Companies Need Cloud Storage
In the rapidly evolving digital landscape of today, cloud storage has emerged as a crucial asset for businesses of all sizes. The shift towards cloud-based solutions is not just a trend but a strategic move that offers numerous advantages. Here are six compelling reasons why companies should embrace cloud storage: Cloud storage offers unparalleled scalability,…
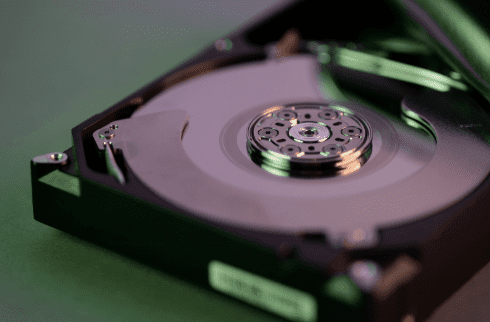
Read MoreHow Much Device Storage You Need: A Comprehensive Guide
Device storage decides how many applications, photos, and files you can retain on your device. When you run out of storage, it can affect your productivity and device performance. But finding the right storage amount isn’t always easy. We can underestimate what we need or get too much storage. This guide will help you figure…
Read More8 Considerations Before Buying Used Technology
We use our devices every day, so they need to work well for our needs. A device that’s slow or broken is inconvenient and can affect productivity for day-to-day tasks. But buying a brand new phone or laptop isn’t always the best option. We’ll cover eight things you should consider before making the purchase of…
Read MoreIs It Time for a Device Upgrade? Check for These 7 Signs
Since older devices usually go for less on the market, repair costs can add up quickly. For example, if you break the screen on your iPhone X, it can cost more than $300 to repair it. An iPhone X can be purchased for around $175. These repair costs are more than the value of the…
Read MoreSpotting the Difference Between Malware and Ransomware
Malware and ransomware are two types of bad software. They can damage your computer or steal your data. Downloading this harmful software comes with serious consequences. In 2024, there were more than 60 million new strains of malware found on the internet. This is why it’s critical to understand the difference between them. This article…
Read More8 Ways to Organize Your Devices for Productivity
Our devices are a big part of our daily lives: work, fun, and staying in touch. Still, sometimes they make us less productive. In this article, you will learn how to organize your device. You’ll learn ways to boost your productivity and get more done. Why is device organization important? Messy devices slow us down and make…
Read MoreHow to Minimize Ransomware Damage
Ransomware has now become a big problem for many people and businesses. It can lock up your files and make you pay money to get them back. This article will show how one can protect themselves from ransomware and what to do in case of an attack. What is Ransomware? Ransomware is a type of…
Read MoreHow to Spot Hidden Malware on Your Devices
Malware is bad software that can hurt your computer or phone. It can also make your device run slow and steal your info.Here is how you can spot hidden malware on your devices. What is Malware? The word “malware” is short for “malicious software.” It is a program that tries to harm your device or…
Read More10 Steps to Prevent a Data Breach
Data breaches can harm your business. They can cost you money and trust. Let’s look at how to stop them from happening. What is a data breach? A data breach is when someone steals information. This can be names, emails, or credit card numbers. It’s bad for your customers and your business. Why should you…
Read More